11 Ways to Keep Data Safe from Ransomware (+1 Free Graphic)
11 Ways to Keep Data Safe from Ransomware
You may think holding someone or something for ransom seems pretty outdated and only for those in high status positions, but holding someone’s information for ransom in a ransomware attack is still extremely common and can happen to anybody (even us average joes), especially in today’s age where everything is digital. While some individuals can be big targets for ransomware, corporations are the much bigger fish to fry.
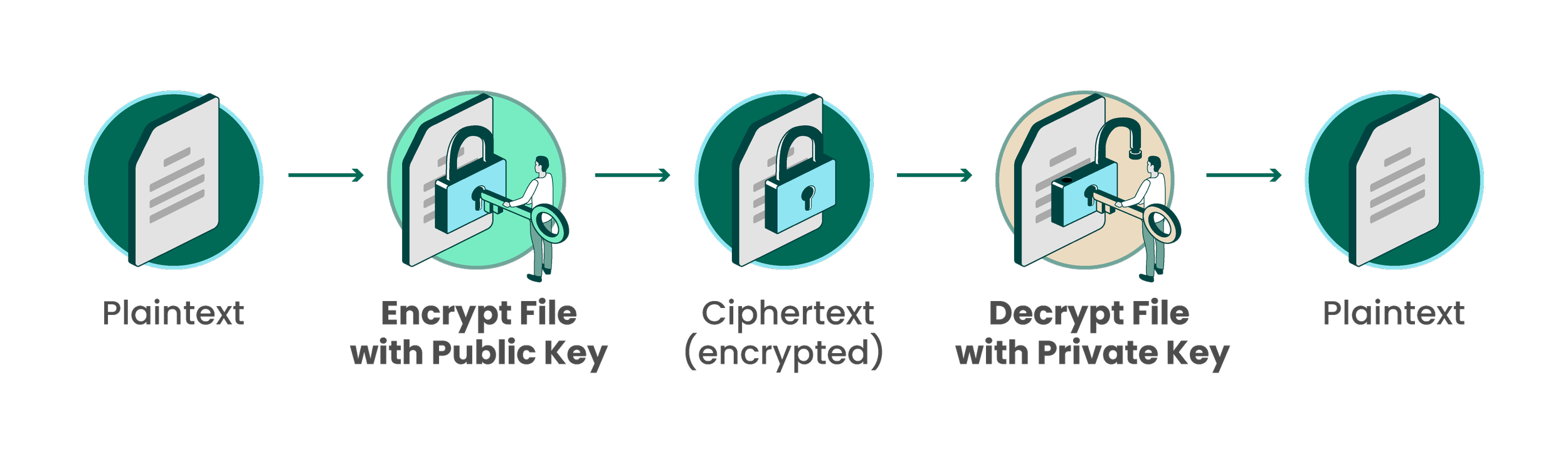
New to ransomware? Ransomware is malware that can affect a target’s device (which can be your personal computer or whole server infrastructure) and hold things “hostage”, or block access to certain things on your device in exchange for money. Hackers can do this by encrypting files on the device, rendering them useless to the end user. This can be financial information, sensitive documents, or even the whole system. Thankfully, there are multiple ways to help protect yourself and your corporation safe from a ransomware attack. This is not an exhaustive list, but it is some of the major steps that should be taken for data protection. Make sure you stick around until the end where you can download our informational graphic for free!
Here are 11 different ways you can keep your data safe to protect against ransomware (+1 Free Graphic):
Take an Initial Security Assessment
Set up filters for Email Spam, Phishing, and Malware
Apply Policies for Password Security
Train Users for General Security Awareness
Stay up to date with Computer Updates
Require Multi-factor Authentication
Deploy Endpoint Security
Enable your Firewalls
Encrypt All Data
Backup your Backup’s Backups
Deploy a MDM (Mobile Device Management)
1. Take an Initial Security Assessment
To start things off, conducting an initial security assessment to determine a personal or company baseline security posture is essential before making any sort of changes. Once a baseline is established, regular assessments conducted to evaluate the company’s continued security posture are crucial. After all, what would be the point of getting a benchmark if you never compare it?
With a good baseline, you can now use that to find current vulnerabilities to protect your systems.
2. Set up filters for Email Spam, Phishing, and Malware
Most attacks originate through email, with phishing attacks being the most common way that a company is compromised. Email filters to remove spam, phishing attempts, and malware will help keep your inbox clean, while password managers will help against credential stuffing tactics. More on that next.
3. Apply Policies for Password Security
Make use of strong passwords, and apply strong password policies on your network! As annoying as they are, they’re for the benefit of everyone. Everyone is at risk if the network or server gets taken over by ransomware. The entire server system could be taken for hostage, and all those essential files along with it. Take the necessary steps to stay protected. For passwords specifically, a great way to do this is to make frequent use of a password manager in order to generate complex, unique passwords for every site that is visited, without having to remember them or write them down on pieces of paper or sticky notes on their desk. We strongly recommend Bitwarden as a password manager. We even wrote about how you can use Bitwarden to protect yourself.
Applying other security policies on your general network can also help protect your users and your data. For example, setting user screen timeouts, limiting certain access for administrative and more can help keep everyone’s data safe.
4. Train Users for General Security Awareness
Require security awareness training for all employees and require it often. This will include email security and how to determine if an email is legitimate or a hook for a phishing attack. If you haven’t been working in IT long, you may think a general computer and web security training class is overkill, but trust me, it’s not. You’ll see as soon as you start working with some of your less technologically advanced friends. And don’t only train them on general cyber safety practices, train users on the company’s policies and procedures for computer and internet usage as well. You never know who might be the next one to try and download a hacked version of WoW on their work computer. It’s important to take regular assessments of everyone’s security aptitude to ensure that all employees know the warning signs of cyberattacks.
5. Stay up to date with Computer Updates
Yes, there is actually a reason Microsoft pushes out regular updates for their systems. Oftentimes these operating system updates patch security bugs in your existing system, which is why it’s important to keep computers up to date. And it’s not just the OS that does this: applications also update to mitigate potential vulnerabilities in their software. Regular reporting and validation of updates to ensure everything has been deployed and mitigated helps prevent bad actors from exploiting existing vulnerabilities when they attack your system. So if you’ve got one or two (or a lot more) team members who absolutely refuse anything to do with updates, you might need to have a chat with them about digital herd immunity.
6. Require Multi-factor Authentication
Require MFA in all places that it is supported. As inconvenient as this may be, MFA adds an additional protection so that even if a hacker has the user’s password, they still cannot access a team’s data. Pair MFA with a password manager and you’ve got an extremely strong digital barrier that will deter most malicious attacks. MFA will also help tremendously against various phishing attacks.
7. Deploy Endpoint Security
Protect computers and data from malware, viruses, ransomware, and cyber attacks by deploying endpoint protection software on all devices, not just your servers. This ensures that all systems have active protection to fight off potential attackers, instead of being completely swept over during a digital attack. Modern endpoint security can even analyze the behavior of processes on the computer to allow them to better detect zero-day attacks. Zero-day attacks are vulnerabilities that are in a system or software that are unknown to even the developer. Once they are discovered by a hacker, there are zero days to prepare against this kind of attack since the vulnerability is built into the program itself and the developers are not even aware of it. These attacks are difficult to detect manually, but the danger can be mitigated with endpoint security that can help detect these kinds of issues. Advanced Endpoint Security replaces outdated antivirus solutions and can even protect against script based threats.
8. Enable your Firewalls
Enable firewalls on all of your devices, and secure them to prevent local machine access both on the company network and when on a public network. That way even if a hacker gains access to a company device or through a public network, your server stays protected. Deploy a network firewall to ensure all internet traffic is secured and minimize the ability for malicious traffic to enter the corporate network. Social engineering is oftentimes a hackers greatest weapon, and they can gain physical entry into your office where they will wreak havoc on your company servers and data unless there is a network firewall to stop them. Log all firewall traffic so you are able to detect and track an attacker should they attempt to get in.
9. Encrypt All Data
Encrypt all data, even if you think there’s no reasonable way for someone to intercept the signal. There are many different tools that bad actors can buy very easily on sites like Amazon that can intercept signals. And without any sort of encryption, you’ve made their job incredibly easy. Deploy device encryption on all endpoints so that company data is encrypted at rest. This helps ensure that even if a computer is stolen or a signal is intercepted, the thief is unable to access company data.
10. Backup your Backup’s Backups
Ensure that all company data is backed up with multiple copies and offsite backups. Many professionals recommend the 3-2-1 strategy, which means that you have 3 copies of your data: 2 stored on different types of media, with 1 backed up on an offsite location. Setup a schedule so data is backed up regularly and is not delayed or impeded by other actions. Test backups often to ensure that they are capable of being restored. This is crucial! There is no point to having a backup if it doesn’t work in your time of dire need.
11. Deploy a MDM (Mobile Device Management)
Mobile Device Management solutions such as Intune ensure that devices are fully managed and locked down as much as possible. The ‘mobile’ part of this strategy is a little misleading. MDM can include mobile devices such as phones, tablets, computers, and more, but it more generally means mobile as in ‘not centralized or stationary’ (hopefully I didn’t freak anyone out who thought “they’re going to manage my personal smartphone?”) MDM allows for security controls and updates to be applied to multiple devices at once, and can even allow for remotely wiping a computer in the event that it is stolen. Microsoft Intune is a great Microsoft built in option for this.
With these strategies in place, your data will be much safer and less at risk during an attack. However it’s important to remember that these strategies lose effectiveness if they are not regularly monitored and updated. A one-and-done kind of approach is not enough in a world where cyber threats are constantly evolving. Stay on your toes! And next time you take your company laptop to the airport and start connecting to their free wifi, at least make sure you have these safeguards in place. Or don’t. Then you’ll really understand why us IT professionals go through all the trouble.
Want to always remember these safeguard strategies? Download our free graphic by filling out the form below.